Connecting to clusters
For the complete documentation index see: llms.txt
All documentation pages available in markdown.
Aerospike Voyager connects to one or more Aerospike clusters and saves each connection profile locally. This guide covers every option in the connection dialog.
A connection in Voyager has two phases: first you create and save a connection profile (cluster address, credentials, TLS), then you connect to open a live session. After saving, you can test connectivity, disconnect, reconnect, edit, or remove the profile.
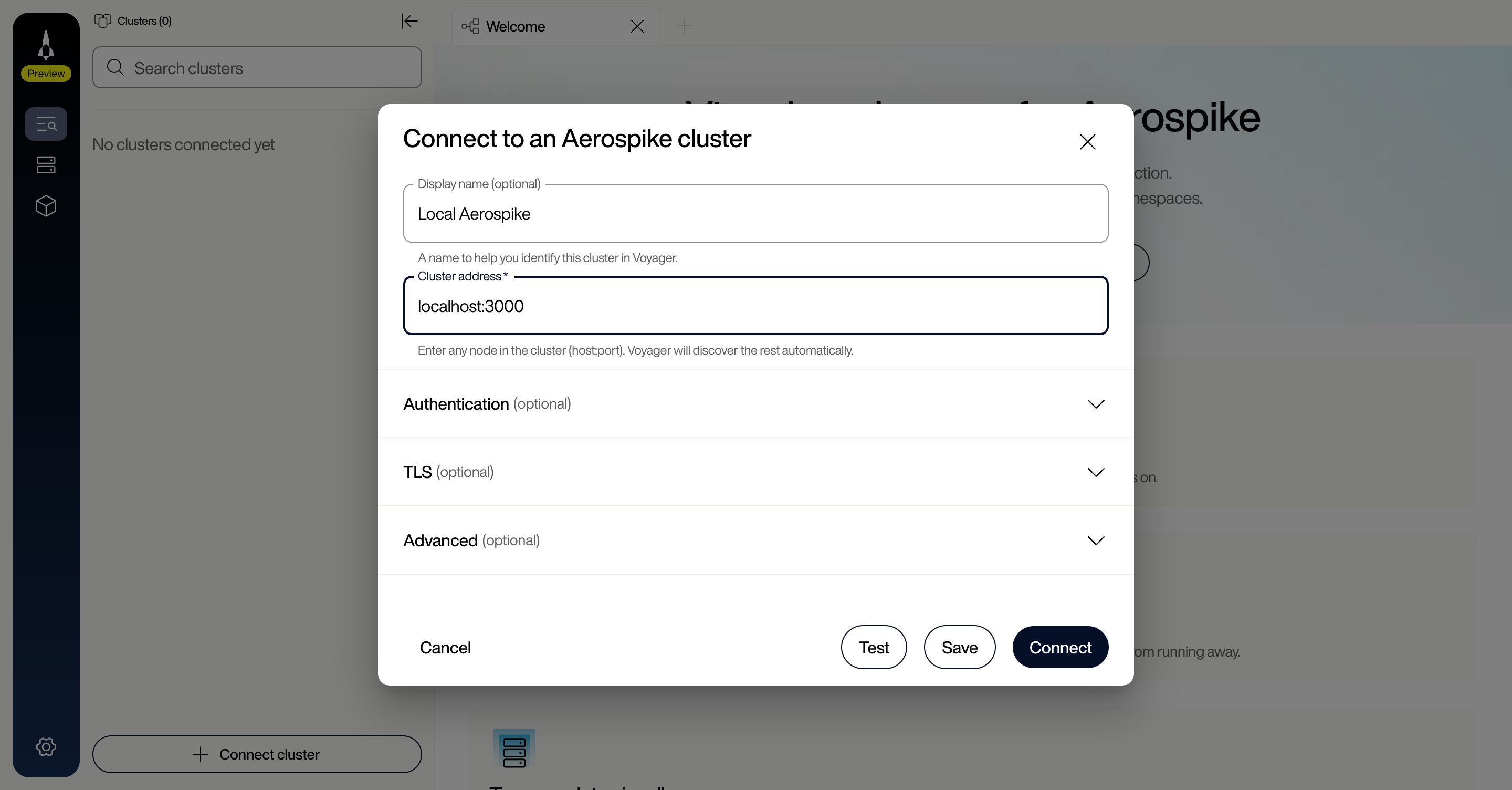
Creating a connection
- On the Welcome page click Connect cluster, or in the connections sidebar click Connect cluster (when no clusters exist) or Add connection (when one or more clusters are saved).
- Enter a Display name (optional label, such as “Dev Cluster” or “Staging”).
- Enter the Cluster address as
host:port. Provide any one node in the cluster; Voyager discovers the rest automatically. To seed with multiple addresses, use a comma-separated list (host1:port1,host2:port2). - Click Test to verify connectivity.
- Click Save to keep the profile, or Connect to save and open a live session.
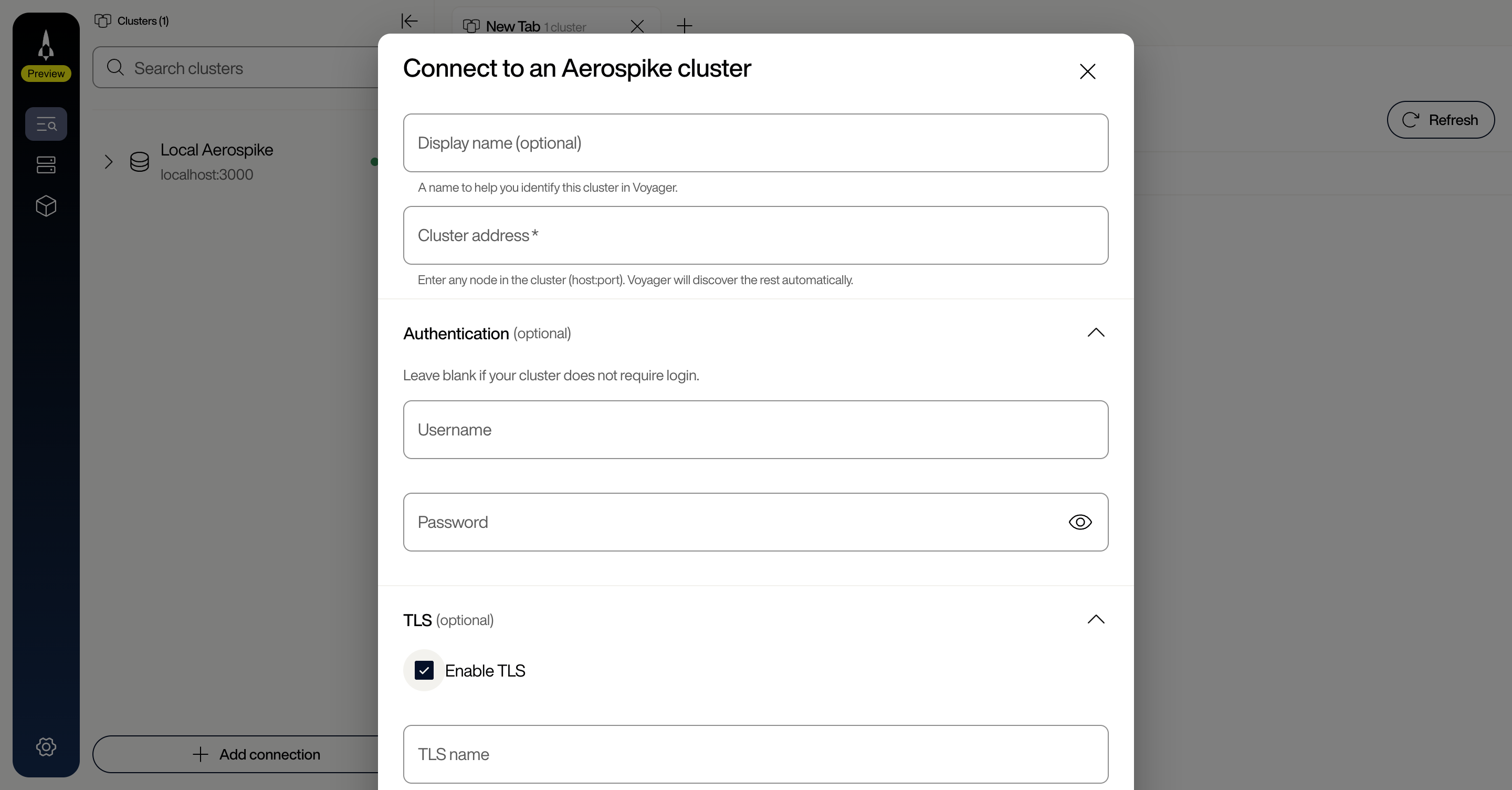
Authentication
If your cluster requires authentication, enter a Username and Password in the connection dialog. These fields are optional for unsecured clusters.
Voyager encrypts all stored credentials (passwords, TLS keys) at rest using AES-256-GCM. The root encryption key is stored in your operating system’s keychain:
- macOS: Keychain
- Windows: Credential Manager
- Linux: Secret Service (using libsecret)
TLS connections
To connect to a TLS-secured cluster:
- Open the TLS section of the connection dialog and check Enable TLS.
- Configure the following fields as needed:
| Field | Description |
|---|---|
| TLS name | Server name used for TLS verification. Must match the name in the server’s certificate. |
| CA certificate | The certificate authority file used to verify the server. Accepts .pem, .crt, or .cer files. |
| Client certificate | Your client certificate for mutual TLS (mTLS). Accepts .pem, .crt, or .cer files. |
| Client key | The private key matching your client certificate. Accepts .pem or .key files. |
| Allow insecure TLS | Bypasses validation of the server’s certificate and hostname. Data remains encrypted, but the client does not verify the server’s identity. Useful for testing with self-signed certificates; leaves the connection vulnerable to man-in-the-middle attacks. Not recommended for production. |
Example: mutual TLS configuration
A typical mTLS setup for a production cluster uses all three certificate fields:
- Check Enable TLS.
- Set TLS name to the common name (CN) or subject alternative name (SAN) in your server certificate (for example,
aerospike.example.com). - Upload your CA certificate (the root or intermediate CA that signed the server certificate).
- Upload your Client certificate and Client key (issued by a CA the server trusts).
- Leave Allow insecure TLS unchecked.
- Click Test to verify the TLS handshake succeeds.
Services alternate
In the Advanced section, check Use services alternate when your cluster nodes advertise different addresses for internal and external access. This is common in:
- Multi-NIC environments where cluster-internal traffic uses a private interface
- NAT or port-forwarding setups (Docker with mapped ports, cloud environments with public/private addresses)
When enabled, Voyager uses the alternate address list advertised by each node instead of the default access address.
Testing a connection
Click Test at any time before saving. Voyager attempts to connect with the current settings and reports success or failure, letting you verify hostnames, credentials, and TLS configuration before committing.
Connection timeout
The default connection timeout is 30 seconds (range: 1-9999). Adjust the Timeout (secs) field in the Advanced section if your cluster is behind a high-latency link.
Managing connections
Right-click a cluster in the sidebar, or click the actions menu (⋮), to access connection actions. The available actions depend on the connection state:
When connected:
- Disconnect: Close the active connection while keeping the profile saved.
- Remove cluster: Permanently delete the connection profile.
When disconnected:
- Edit connection: Modify connection settings (host, port, credentials, TLS).
- Connect: Re-establish the connection.
- Remove cluster: Permanently delete the connection profile.
Connection status indicators
Each connection displays a status indicator (the colored dot next to the cluster name in the sidebar):
| Status | Meaning |
|---|---|
| Disconnected | Connection profile exists but is not active. |
| Connecting | Voyager is attempting to establish a connection. |
| Connected | Connection is active and healthy. |
| Error | Connection attempt failed or an active connection was lost. |
Multiple connections
Each saved profile is independent. You can open and switch between multiple active connections; each maintains its own session.